
Intel & AMD are worried because they are bound to take severe hits on both the public image side and the stock markets. The researchers and security folks are worried that the next major malware is going to hit every computer ever made in the last 20 years.
You should be worried because this whole fiasco will hurt you, one way or the other. Your processor will slow down after it is patched and you will have to be carefull about the next malware attack. And there is no way around either.
All of the variants of this underlying vulnerability involve a malicious program gaining access to data that it shouldn’t have the right to see, and do so by exploiting two important techniques used to speed up computer chips, called speculative execution & caching.
Is the CPU in the computer that you have at work and office affected ? In short, yes !
Spectre and Meltdown are variations of the flaw that affects nearly every CPU manufactured in the last 2 decades. The flaws are so basic and widespread that security researchers are calling them catastrophic.
What is the difference between Meltdown and Spectre ?
If you are technically inclined to dig into how Spectre and Meltdown work, you should check out the post on Google’s Project Zero site. To keep it short and simple, both Spectre and Meltdown could allow potential attackers to get access to data they shouldn’t have access to using the techniques outlined above, but their effects are somewhat different:
Meltdown

Meltdown breaks all security assumptions on virtualization and memory space isolation from the last 20 years.
The security of computer systems fundamentally relies on memory isolation of the kernel, they are marked as non-accessible and are protected from user access. Meltdown exploits side effects of out-of-order execution on modern processors to read arbitrary kernel-memory locations including personal data and passwords.
This is a pretty severe problem, but the fixes are slowly starting to roll out. By exploiting the flaw, an attacker can use a program running on a machine to gain access to data from all over that machine that the program shouldn’t normally be able to see, including confidential data belonging to other applications and passwords that only administrators should have access to.
Spectre

The name does not come from the James Bond Movie, but the effect is equally spectacular. And the vulnerability is such that the attacks can change form over the yeras.
Modern processors use branch prediction and speculative
execution to maximize performance. CPUs try to guess
the next work and attempt to execute ahead. When the
predicted work or some other form of it finally arrives, the CPU either discards or commits the speculative computation. Speculative logic is not bound to need, it can access to the victim’s memory and registers, and can perform operations with measurable side effects.
Spectre attacks involve inducing a victim to speculatively perform operations that would not occur during correct program execution and which leak the victim’s confidential information via a side channel to the adversary.
Do Spectre and Meltdown patches hurt performance?
These patches generally fix the vulnerabilities by altering or disabling how software code makes use of the speculative execution and caching features built into the underlying CPU. The downside of this is that because these features were designed to improve system performance, working around them can and will slow down your systems.
While the initial reports spoke of performance hits of up to 30 percent, benchmarks from seem to indicate that 5 to 10 percent slowdown is going to be the Norm.
Intel
Intel CEO Brian Krzanich has penned an open letter to the rest of the technology industry, addressing concerns over the two major CPU security flaws. The company says it’s ready to be transparent. “As we roll out software and firmware patches, we are learning a great deal,” admits Krzanich. “We know that impact on performance varies widely, based on the specific workload, platform configuration and mitigation technique.”
Intel is committing to providing updates for at least 90 percent of CPUs produced in the last five years by January 15th, and the rest by the end of January.
Whether end users will get those updates is another story, as most PC makers have poor update systems in place for firmware updates.
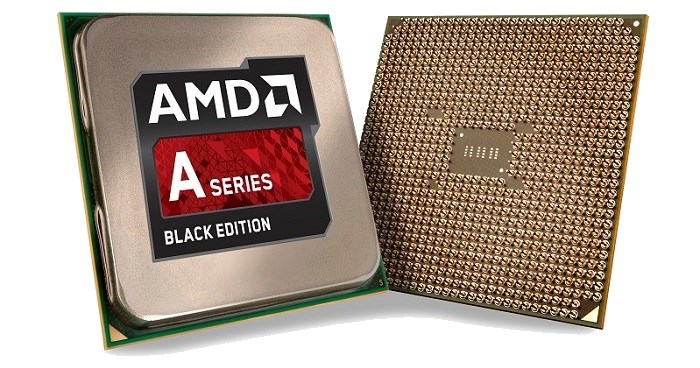
AMD
AMD’s initial response to the Meltdown and Spectre CPU flaws made it clear “there is a near zero risk to AMD processors.” That zero risk doesn’t mean zero impact, as we’re starting to discover today.
AMD is making firmware updates available for Ryzen and EPYC owners this week, and the company is planning to update older processors “over the coming weeks.” Like Intel, these firmware updates will be provided to PC makers, and it will be up to suppliers to ensure customers receive these.
AMD isn’t saying whether there will be any performance impacts from applying these firmware updates, nor whether servers using EPYC processors will be greatly impacted or not.
Caught between the Fire and the Frying Pan
Intel’s Spectre patch is causing reboot problems for older processors
Intel Says, “We have received reports from a few customers of higher system reboots after applying firmware updates. Specifically, these systems are running Intel Broadwell and Haswell CPUs for both client and data center. We are working quickly with these customers to understand, diagnose and address this reboot issue”
The notice comes even as Intel has been quietly advising its customers not to install the latest firmware updates. Based on a document that Intel has been sending out, they recommend that customers “delay additional deployments of these microcode updates” while it figures out the reboot issue.
What Next ?
Hold tight and keep your eyes and ears open to see how this is going to play out. At the moment, I would recommend that you do not install any immediate patches on your system as soon as they roll out.
Wait and watch and stay a little behind the update curve. Let the circus play out and watch from the sidelines till there is clarity.

Recent Comments